Table of Contents
- What is HIPAA Compliant File and Data Storage?
- What are the Top 10 Considerations for HIPAA Compliant File Storage?
- 1 - Know that the data is covered by HIPAA.
- 2 - Understand that simply stating compliance is insufficient.
- 3 - Study the Security Rule.
- 4 - Know how encryption will occur.
- 5 - Perform and prepare for risk assessment.
- 6 - Get a strong business associate agreement.
- 7 - Check the service level agreement.
- 8 - Require a 24/7 on-site monitoring staff.
- 9 - Require internal and external training.
- 10 - Go beyond HIPAA.
- HIPAA-compliant, access-controlled hosting
What is HIPAA Compliant File and Data Storage?
Storing your files data in a HIPAA-compliant manner requires careful consideration of the parameters of the HIPAA law and the ways in which the organization is specifically adhering to its requirements for comprehensive safeguards.
What are the Top 10 Considerations for HIPAA Compliant File Storage?
File storage is one of the key concerns of HIPAA. Here are ten recommendations to guide your adoption of systems that meet the parameters of the federal healthcare law.
- Know that the data is covered by HIPAA.
- Understand that simply stating compliance is insufficient.
- Study the Security Rule.
- Know how encryption will occur.
- Perform and prepare for risk assessment.
- Get a strong business associate agreement.
- Check the service level agreement.
- Require a 24/7 on-site monitoring staff.
- Require internal and external training.
- Go beyond HIPAA.
1 – Know that the data is covered by HIPAA.
Understanding the scope of protected health information (PHI) is a key first question since this will determine if the healthcare law is relevant or not. If the data has been de-identified, it is no longer PHI, because PHI is personally identifiable. (Electronic PHI is also called ePHI.) Typically in order for a cloud provider or other firm to sign a business associate agreement (BAA) with a covered entity, they will demand that ePHI be encrypted in order to store it. Note that the Department of Health and Human Services has clarified a BAA is necessary for all relationships that involve PHI, even if the data is encrypted and the provider does not have a key.
2 – Understand that simply stating compliance is insufficient.
Many cloud providers and other vendors will indicate that their systems are “HIPAA-compliant.” Keep in mind that all a provider can do is establish a setting that permits HIPAA-compliant data treatment. The organization that is using a cloud system will ultimately determine if the method is compliant since a big part of HIPAA is following the rules for use and configuration that adhere to administrative safeguards.
3 – Study the Security Rule.
A strong HIPAA-compliant setting is built on following the mandates of the Security Rule, which puts the rights of the Privacy Rule into effect through the requirement to implement administrative, technical, and physical safeguards to protect ePHI.
Compliance with the HIPAA Security Rule is achieved through the following steps:
- Ensure that your staff knows and is adherent to HIPAA law.
- Make sure that the privacy, integrity, and availability of any ePHI you store is upheld, as with all ePHI you transmit, receive, or create.
- Implement protections to mitigate reasonably foreseen risk to the data.
- Establish defenses to avoid unauthorized and reasonably anticipated disclosure or use.
See below on risk assessment, another requirement of the Security Rule.
4 – Know how encryption will occur.
You must use encryption (or an equivalent alternative) for any data exchanges between the cloud and other systems, including your onsite and cloud-hosted apps. FIPS-14-2 encryption is the standard to use for the transmission of ePHI. There should also be at-rest encryption in place for local hard drives, storage area networks (SANs), and backups.
5 – Perform and prepare for risk assessment.
Risks to any system used for HIPAA-compliant file storage should be analyzed routinely. The steps to that process are as follows:
- Analyze the system for risks, what the possible impacts of compromise would be, and the likelihood of particular risks happening.
- Implement security methods to protect against the risks that you have identified.
- Document the security measures as you adopt them. If anything is nonstandard (i.e., skipping encryption for a functionally equivalent alternative), give your reasoning.
- Install and maintain reasonable, appropriate, and continuous protection. The risk assessment should direct you toward administrative, technical, and physical measures that make sense given the environment.
- Regularly conduct risk assessments to assess how your risk profile has changed and how well your current environment is working. While an annual comprehensive risk assessment is considered standard by many in the industry, HHS Department risk analysis guidance notes that conducting these assessments every two or three years may be appropriate, depending on the setting.
Risk assessment should be viewed as an effort toward continuous improvement, embedded in a compliance culture with ongoing refinement of security awareness.
6 – Get a strong business associate agreement.
Often, rules for HIPAA-compliant file storage are needed relating to relationships with outside entities, particularly cloud service providers (CSPs). While cloud may seem intrinsically problematic for compliance due to its offsite nature, its security has been advocated by many. As early as 2014, researchers were presenting models for HIPAA-compliant hybrid clouds.
As the adoption of cloud technology increases, healthcare organizations must control their partner relationships to protect ePHI in the cloud – and the HHS actually provides guidance specific to the cloud. Business associates and covered entities that decide to store their data with cloud providers or other third-party vendors (e.g. dedicated hosting and colocation scenarios) should understand the provider’s system for its own risk analysis, which should in turn help develop its risk management policy and the terms of the BAA.
Whether you are a covered entity or a business associate, HIPAA compliance mandates a study or assessment of all health data you store – as well as that which you produce, send, and receive – to ensure maintenance of its availability, integrity, and confidentiality. The connection between the risk analysis and business associate agreements cannot be understated, especially in the context of the cloud: the HHS noted directly that public, private, and hybrid clouds can all be HIPAA compliant as long as a BAA is signed, with “the type of cloud configuration… [affecting] the risk analysis and risk management plans of all parties and the resultant provisions of the BAA.”
7 – Check the service level agreement.
Be sure that the service-level agreement from any HIPAA storage provider is aligned with the needs of HIPAA compliance. For example, if the cloud provider is not guaranteeing near-100 percent uptime, the covered entity could, in turn, not be meeting the availability requirement. The SLA should also address safeguards related to ransomware.
8 – Require a 24/7 on-site monitoring staff.
There should be continuous, around-the-clock monitoring of the HIPAA systems managed by a cloud provider to guard against unauthorized access. With oversight of the systems in place at all times, reliability becomes stronger, and the covered entity or business associate is able to respond quickly to any emergent security events.
9 – Require internal and external training.
Whether you are using a cloud environment or your own, training is critical to compliance. With a Verizon study (released in March) finding that more than half of healthcare breaches were due to the insider threat, it is key to know that your employees understand how to stay compliant – especially since the error is the #1 reason for insider breaches. The 2017 Data Breach Investigation Report, which determined this figure through analysis of 1368 security events, found that top insider threats were:
- Error – 33.5%
- Misuse – 29.5%
- Physical threat – 16.3%
- Hacking – 14.8%
- Malware – 10.8%.
Employees of business associates should receive regular training on data security and compliance as well.
10 – Go beyond HIPAA.
HIPAA – and its updated scope under HITECH – are not the only regulatory concerns when considering healthcare file storage. There may be other law that applies as well, based on the type of information, nature of parties to the contract, and terms of the agreement related to data use and storage.
Other regulations to address to determine the possible need for additional compliance are the General Data Protection Regulation (GDPR) from the European Union; personal data privacy rules from the Federal Trade Commission; confidentiality stipulations within “Confidentiality of Substance Use Disorder Patient Records” (Code of Federal Regulations Part 2, Title 42); and state law directing the use and storage of health information.
HIPAA-compliant, access-controlled hosting
Top HIPAA Compliant Cloud Storage Providers:
- Atlantic.Net
- Amazon AWS
- Microsoft Azure
- Google Cloud
- Blackblaze
- Box
- Carbonite
- Dropbox
- IDrive
- Egnyte
At Atlantic.Net, our HIPAA server infrastructure is fully audited and compliant with HIPAA and HITECH, as well as adherent with SSAE 18 (formerly SSAE 16) from the American Institute of Certified Public Accountants. See our HIPAA-compliant cloud storage hosting solutions.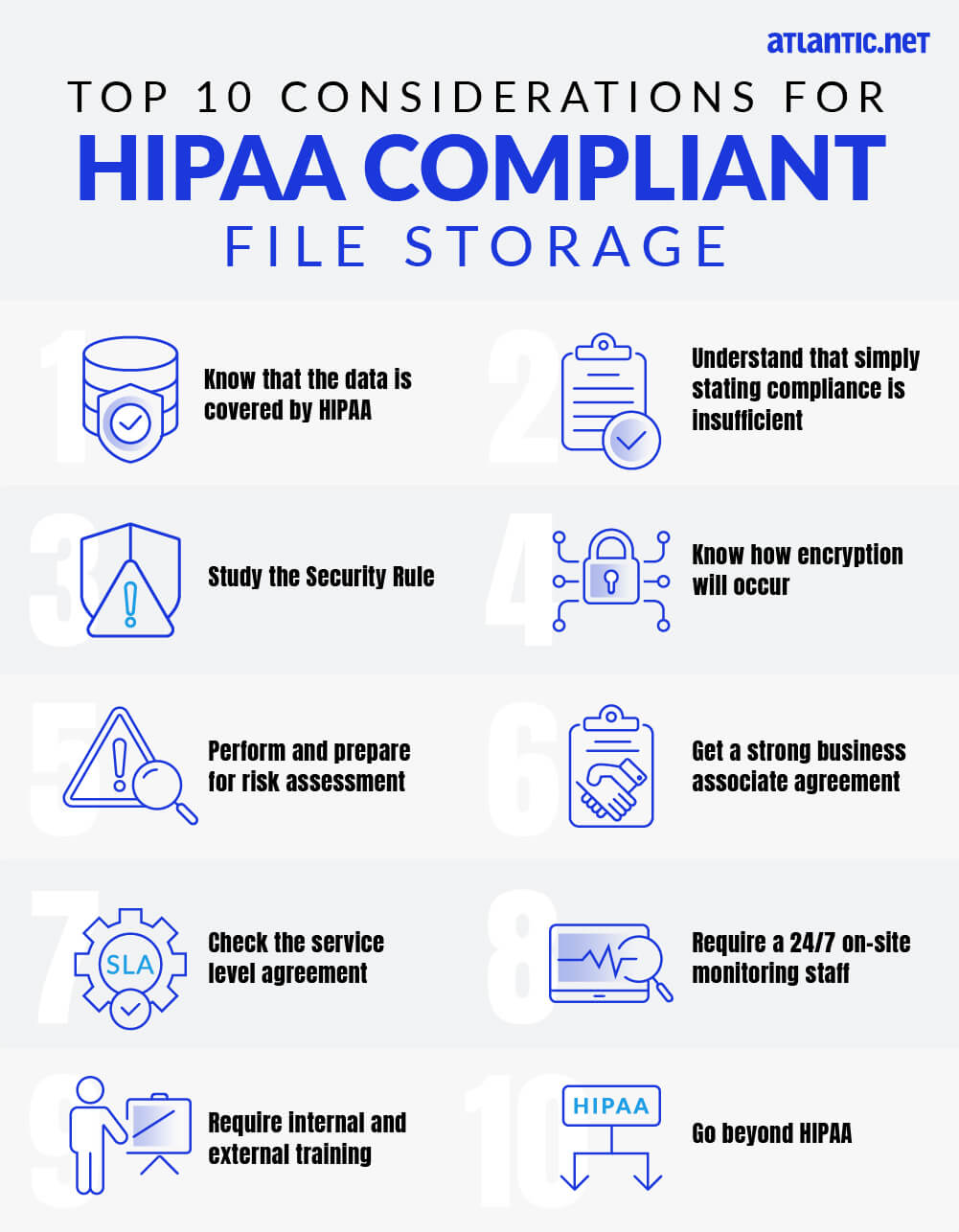
Read More About HIPAA Compliance
- HIPAA Compliance Checklist
- How to Become HIPAA Compliant
- What Is the HIPAA Security Rule?
- HIPAA Data Storage Requirements
- Protecting e-PHI in the Cloud
- What Is HIPAA Cloud Computing?
- What Is Healthcare Hosting?
- What Is PHI?
* This post is for informational purposes only and does not constitute professional, legal, financial, or technical advice. Each situation is unique and may require guidance from a qualified professional.
Readers should conduct their own due diligence before making any decisions.